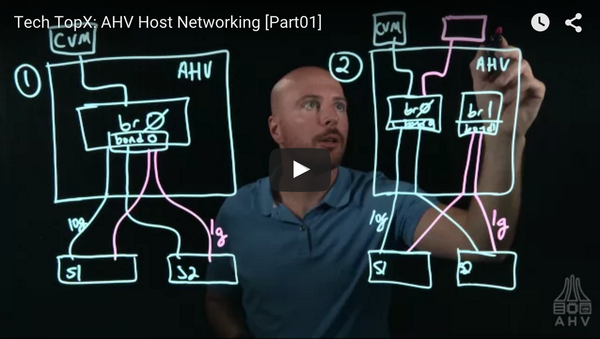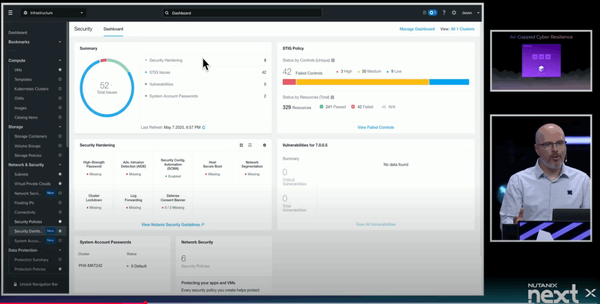
Technology
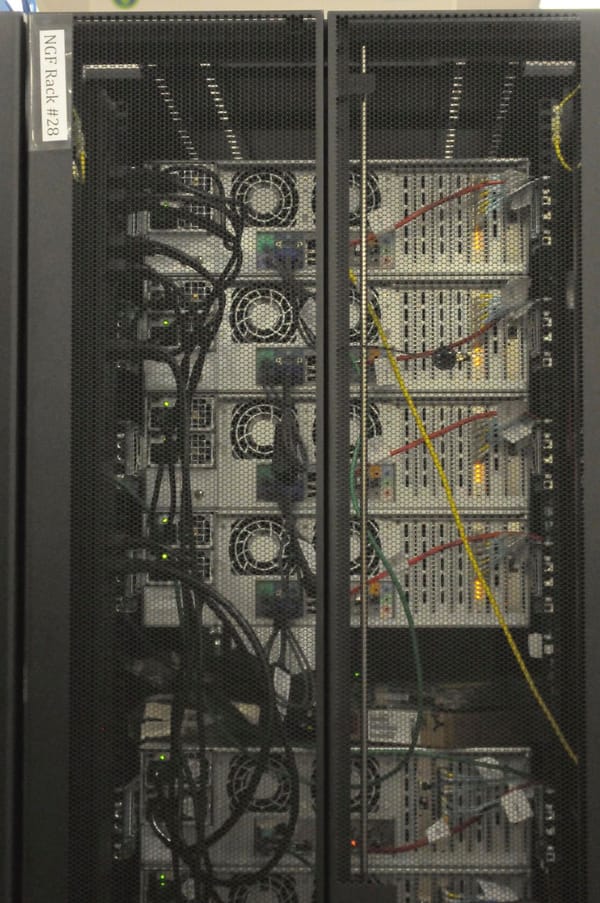
Air-Gapped Cyber Resilient Infrastructure
During Nutanix .NEXT 2025 in Washington, DC, I had the honor of presenting a main stage demo to ~4,000 attendees. I can write a bit more about what it took to get this demo ready, but for now I'm just happy to share that the presentation is