Technology
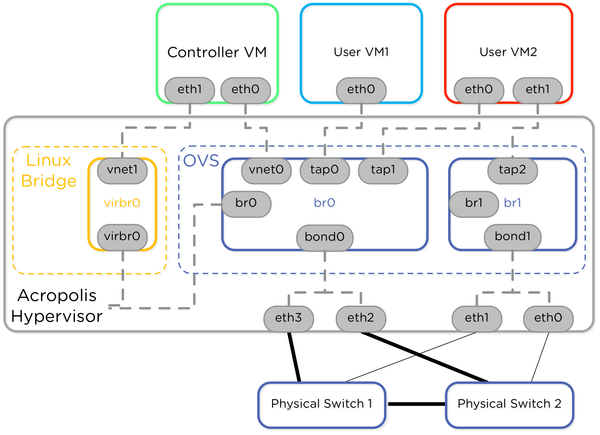
Nutanix AHV Networking - What's New
We just made a bunch of announcements about networking enhancements to AHV, and I'll be posting about them at Nutanix.com. Here's an overview of the series: Part 1: AHV Network Visualization Part 2: AHV Network Automation and Integration Part 3: AHV Network Microsegmentation Part 4: